A data breach is the process in which an organization or a company faces data loss of some important confidential inform...
Sophos Rapid Response has discovered that keeping close tabs on the account credentials in your organization should alwa...
Documents reveal how the Australian Federal Police made use of Clearview AI — a controversial facial recognition technol...
Microsoft’s LinkedIn was sued by a New York-based iPhone user on Friday for allegedly reading and diverting users&...
Australia’s privacy watchdog will probe the personal information handling practices of Clearview AI after several polici...
The NSW government has set up a cyber security vulnerability management centre in Bathurst, which will start operating n...
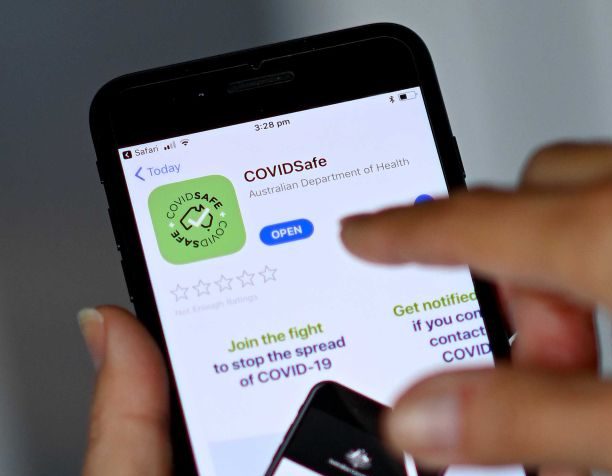
When it launched, COVIDSafe was marketed as Australia’s ticket out of lockdown, so long as everyone downloaded it....
What’s happened? The Australian Government is aware of and responding to, a sustained targeting of Australian government...