Businesses large and small are under threat from increasingly aggressive and brutal ransomware attacks. Loss of access to critical files, followed by a demand for payment can cause massive disruption to an organization’s productivity.Advanced monitoring agent handle backup files to control data.
But what does a typical attack look like? And what security solutions should be in place to give the best possible defense?
This article examines commonly used techniques to deliver ransomware, looks at why attacks are succeeding, and gives nine security recommendations to help you stay secure. It also highlights the critical security technologies that every IT setup should include and advanced monitoring agents handle backup files to control data.
Ransomware – a brief introduction
Ransomware is one of the most widespread and damaging threats that internet users face. Since the infamous CryptoLocker first appeared in 2013, we’ve seen a new era of file-encrypting ransomware variants delivered through spam messages and Exploit Kits, extorting money from home users and businesses alike.Advanced monitoring agents can handle backup files.
The current wave of ransomware families can have their roots traced back to the early days of Fake AV, through “Locker” variants and finally to the file-encrypting variants that are prevalent today. Each distinct category of malware has shared a common goal – to extort money from victims through social engineering and outright intimidation. The demands for money have grown more forceful with each iteration.
A survey of 2,700 organizations found that 54% have been hit by ransomware – twice on average. Of those hit, 77% were running up-to-date antivirus at the time of the attack. And the costs are punitive, with the median impact per organization US$133k (£100k).
Why are ransomware attacks so successful?
Most organizations have at least some form of IT security in place. So why are ransomware attacks slipping through the net?
- Sophisticated attack techniques and constant innovation
- Access to ready-made ‘Exploit as a Service’ (EaaS) programs is increasingly easy, making it simple to initiate, successfully complete and benefit from an attack, even for less tech-savvy criminals. Below is a EaaS program for sale.


- Skillful social engineering is used to prompt the user to run the installation routine of the ransomware. For example you may receive an email that reads something like this: “My organization’s requirements are in the attached file, please provide me with a quote.”
- Producers of ransomware operate in a highly professional manner. This includes providing a working decryption tool after the ransom has been paid, although this is by no means guaranteed.
- Security holes at affected companies
- Inadequate backup strategy (no real-time backups, backups not offline/off-site).
- Updates/patches for operating system and applications are not implemented swiftly enough.
- Dangerous user/rights permissions (users work as administrators and/or have more file rights on network drives than necessary for their tasks).
- Lack of user security training (“Which documents may I open and from whom?”, “What is the procedure if a document looks malicious”, “How do I recognize a phishing email?”).
- Security systems (virus scanners, firewalls, IPS, email/web gateways) are not implemented or are not configured correctly. Inadequate network segmentation can also be included here (servers and work stations in the same network).
- Lack of IT security knowledge (.exe files may be blocked in emails but not Office macros or other active content).
- Advanced monitoring agents specifies the backup files.
- Conflicting priorities (“We know that this method is not secure but our people have to work…”).
- Lack of advanced prevention technology
- Many organizations have some form of generic protection.
- Ransomware is constantly being updated to exploit and avoid this protection. For example, deleting itself so quickly after encrypting files that it can’t be analyzed.
- Solutions need to be designed specifically to combat ransomware techniques.
- We are applying advanced monitoring agents.
How does a ransomware attack happen?
There are two main ways that a ransomware attack starts. Via an email with a malicious attachment, or by visiting a compromised (often a legitimate, mainstream) website.
Malicious email
Today’s criminals are crafting emails that are indistinguishable from genuine ones. Grammatically correct with no spelling mistakes, and often written in a way that is relevant to you and your business.


When opened, the zip file appears to contain an ordinary .txt file.
However, when the file is executed the ransomware is downloaded and installed onto your computer. In this example it’s actually a JavaScript file disguised as a .txt file that’s the Trojan horse, but there are many other variations on the malicious email approach, such as a Word document with macros, and shortcut (.lnk) files.
Malicious websites
Another common way to get infected is by visiting a legitimate website that has been infected with an exploit kit. Even popular websites can be temporarily compromised. Exploit kits are black market tools that criminals use to exploit known or unknown vulnerabilities (such as zero-day exploits).
You browse to the hacked website and click on an innocent-looking link, hover over an ad or in many cases just look at the page. And that’s enough to download the ransomware file onto your computer and run it, often with no visible sign until after the damage is done.
What happens next?
After initial exposure such as via the email and web examples, the ransomware takes further action:
- It contacts the attacker’s Command & Control server, sending information about the infected computer and downloading an individual public key for it.
- Specific file types (which vary by ransomware type) such as Office documents, database files, PDFs, CAD documents, HTML, XML, etc., are encrypted on the local computer, removable devices and all accessible network drives.
- Automatic backups of the Windows operating system (shadow copies) are frequently deleted to prevent data recovery.
- A message appears on the desktop explaining how the ransom can be paid (typically in Bitcoins) in the specific time frame.
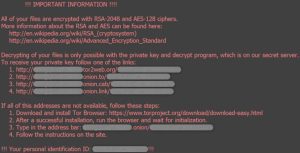
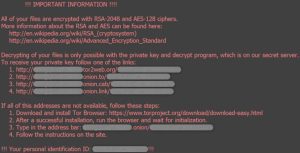
- Finally, the ransomware deletes itself leaving the encrypted files and ransom note behind.
- advanced monitoring agent provides the best results according to the demands.
Ransomware Evolved
One of the first major ransomware outbreaks was the CryptoLocker ransomware which appeared in 2013. CryptoLocker infected hundreds of thousands of machines, earning millions of dollars for the attackers. It eventually was shut down when the Gameover Zeus botnet, which was used to distribute the attacks, was taken offline. CryptoLocker was followed by variants such as CryptoWall, TeslaCrypt, and Cerber.
In 2017 ransomware gained global attention with the outbreak of WannaCry. The attack was launched using suspected NSA code that was leaked by a group of hackers known as the Shadow Brokers. It used a variant of the ShadowBrokers APT EternalBlue Exploit (CC-1353). WannaCry was followed by another high profile attack, Petya or NotPetya. This attack is believed to be a nation-state attack started by Russia. Unlike file-based encryption ransomware, Petya was a “wiper” ransomware attack which encrypted the Master Boot Record causing significant damage to the device.
After WannaCry, attackers became even more ruthless with their attacks, focusing on specific targets such as businesses, hospitals, schools, and government agencies, rather than just a “spray and pray” approach. Some of the more impactful ransomware variants included Emotet and SamSam which used advanced stealthy techniques to get by endpoint defenses. Advanced monitoring agent helps to prevent your systems from attackers.
This has continued in 2019 with Ryuk. Ryuk has leveraged (and stolen) the techniques that have been proven to be successful from previous attackers. Techniques include entering via an exposed Remote Desktop Protocol (RDP), escalating privileges, tampering with security software, and spreading far and wide before executing the payload.
Nine best security practices to apply now
Staying secure against ransomware isn’t just about having the latest security solutions. Good IT security practices, including regular training for employees are essential components of every single security setup. Make sure you’re following these nine best practices:
- Patch early, patch often
Malware that doesn’t come in via a document often relies on security bugs in popular applications, including Microsoft Office, your browser, Flash and more. The sooner you patch, the fewer holes there are to be exploited.
- Backup regularly and keep a recent backup copy off-line and off-site
There are dozens of ways other than ransomware that files can suddenly vanish, such as fire, flood, theft, a dropped laptop or even an accidental delete. Encrypt your backup and you won’t have to worry about the backup device falling into the wrong hands.
- Enable file extensions
The default Windows setting is to have file extensions disabled, meaning you have to rely on the file thumbnail to identify it. Enabling extensions makes it much easier to spot file types that wouldn’t commonly be sent to you and your users, such as JavaScript.
- Open JavaScript (.JS) files in Notepad
Opening a JavaScript file in Notepad blocks it from running any malicious scripts and allows you to examine the file contents.
- Don’t enable macros in document attachments received via email
Microsoft deliberately turned off auto-execution of macros by default many years ago as a security measure. A lot of infections rely on persuading you to turn macros back on, so don’t do it!
- Be cautious about unsolicited attachments
The crooks are relying on the dilemma that you shouldn’t open a document until you are sure it’s one you want, but you can’t tell if it’s one you want until you open it. If in doubt leave it out.
- Don’t give yourself more login power than you need
Don’t stay logged in as an administrator any longer than is strictly necessary and avoid browsing, opening documents or other regular work activities while you have administrator rights.
- Stay up-to-date with new security features in your business applications
For example Office 2016 now includes a control called “Block macros from running in Office files from the internet”, which helps protect against external malicious content without stopping you using macros internally.
- Patch early, patch often!
Staying on top of patches is so important that we’ve included it twice. Don’t let ransomware exploit vulnerabilities that have patches available!
How can we protect you from ransomware?
To stop ransomware you need to have effective, advanced protection in place at every stage of an attack.
Securing your endpoints
We use multiple layers of defence to stop ransomware in its tracks. Anti-exploit technology stops the delivery of ransomware, deep learning blocks ransomware before it can run and CryptoGuard prevents the malicious encryption of files, rolling back affected files. It works alongside your existing antivirus from any vendor.And prevents advanced monitoring agent.
Protecting your servers
Server Advanced includes CryptoGuard functionality to prevent the malicious encryption of your files, rolling back affected files. Whitelisting and lock down permits only authorized applications and identifies what they can change – all other attempts to make changes are blocked. Malicious traffic detection stops ransomware from contacting command & control servers and downloading the payload.Advanced monitoring agent control malicious application.
Stop phishing emails
Phish Threat sends simulated phishing attacks to your organization, testing preparedness against real world attacks. Emails can be customized to your organization and industry and have been carefully localized for multiple languages. Detailed feedback lets you see how many users failed, overall susceptibility to attacks and more.Is Advanced monitoring agent are workable?
Are you infected with ransomware?
Looking for a solution?
Don’t worry, Computer Support Professionals have got you covered.
Contact us at 1300 660 368 and get rid of ransomware in no time.




