Australia’s privacy watchdog will probe the personal information handling practices of Clearview AI after several polici...
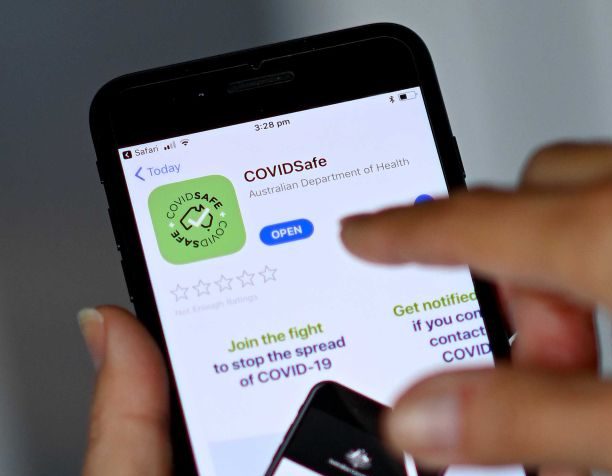
When it launched, COVIDSafe was marketed as Australia’s ticket out of lockdown, so long as everyone downloaded it....
What’s happened? The Australian Government is aware of and responding to, a sustained targeting of Australian government...
A new technology that could help alert people who have been in close contact with someone who has COVID-19 is being test...
COVIDSafe was sold by the Government as essential to lifting coronavirus lockdown restrictions, but the app is yet to pr...
A Dutch master’s student has found vulnerabilities in the Thunderbolt input/output port hardware design that lets ...
Microsoft warns to stay alert from human-operated ransomware campaigns During the pandemic crisis, the cybercriminals ar...
Due to COVID-19 pandemic, many organizations and people. We have started using web conferencing systems, like Zoom, Skyp...